APT41
Posted October 4, 2022 by Austin Stevens ‐ 2 min read
APT41 is a Chinese state-sponsored espionage group that also conducts financially-motivated operations. Active since at least 2012, APT41 has been observed targeting healthcare, telecom, technology, and video game industries in 14 countries.
APT41 is highly persistent with its attacks. The group attacked a single target with 150 unique pieces of malware for a year long. They're also able to respond quickly to changes in victim environments. When suspicious activity is noticed and they get kicked from a system, they are able to make their way back in.
Their activity appears to be for personal gain; which appears to be unusual for Chinese state-sponsored groups. In order for them to maintain revenue, "APT41 has manipulated virtual currencies and even attempted to deploy ransomware," states FireEye. They've also targeted developers by breaking into their networks and stealing their digital certificates. This allows them to sign malicious code making it seem legitimate and deploying it to targets.
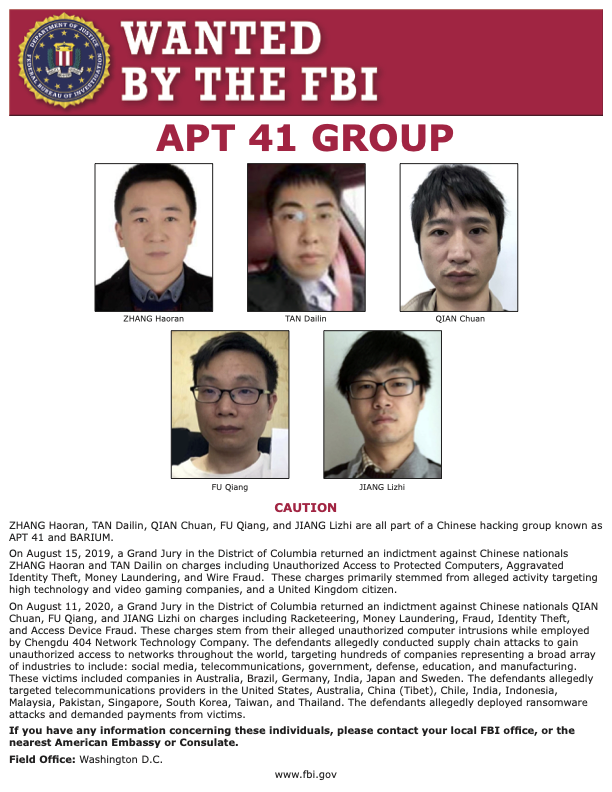
There is no clear understanding if this was sponsored by the Chinese Ministry of State Security or if they turn a blind eye to this activity. The United States Department of Justice in August of 2019 named the group as a threat and brought charges against five Chinese and two Malaysian nationals for allegedly compromising more than 100 companies worldwide.
APT41 can also be known as Double Dragon, Barium, Winnti, Wicked Panda, Wicket Spider, TG-2633, Bronze Atlas, Red Kelpie, or Blackfly.
From the FBI:
On August 15, 2019, a Grand Jury in the District of Columbia returned an indictment against Chinese nationals ZHANG Haoran and TAN Dailin on charges including Unauthorized Access to Protected Computers, Aggravated Identity Theft, Money Laundering, and Wire Fraud. These charges primarily stemmed from alleged activity targeting high technology and video gaming companies, and a United Kingdom citizen.